The evolving science of cybersecurity is rewriting the rules of the old order. New definitions are being cast for enterprise repositories, roles and rigors. To get a grounds-eye view of this new charter, Confluence brought together three leaders driving the change: Vishal Salvi, CISO at Infosys; Mike Wilson, SVP and Chief Security Officer, Molina; and Michael Guenzler, SVP and CISO, Venerable Holdings, Inc.
Key Takeaways

The new CISO archetype emerges
The three faces of the security officer have been technology, regulation and defense. In a hyperconnected world, the new face is more business-relevant than ever: core to products from smart medical devices to smart utility meters.

This is a digital paradigm of ‘zero trust’
Do firewalls hold up when the door is always open? As companies move to a cloud-centric and IoT-driven network, anything that connects is guilty until tagged innocent. The ecosystem of security is built on trusting nothing and securing everything.
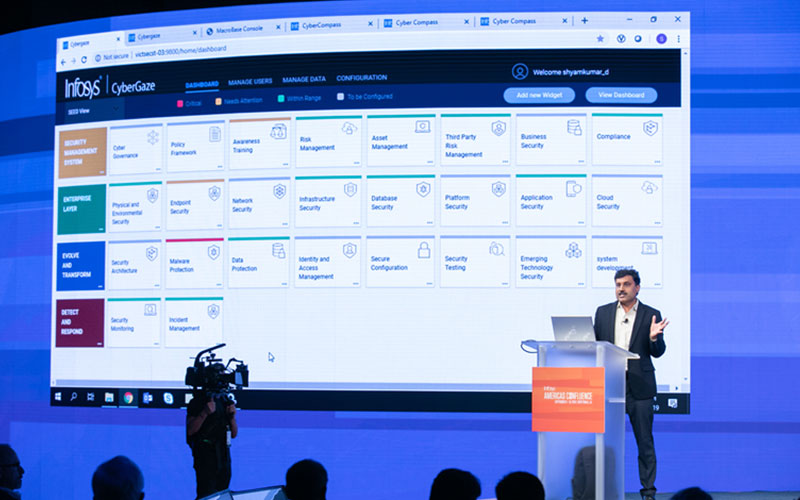
Finding meaning in all the metrics
Step one is putting together all the data to manage security. Step two is looking through the maze and tracing the relevance and impact of each metric to a larger security goal. Step three? Contexts will change, so keep looping back to step two.

From cyber-speak to business-speak
Cybersecurity is a domain that now demands an understandable boardroom lexicon. One where terms like threat vectors and encryption protocols can be translated into balance sheet impact. A language of “what’s at stake”.
The movement of our end points to the edges that we hadn't predicted in the past like IoT, OT, and manufacturing areas are getting connected in ways that we hadn't thought about before. It's driving us to a new security paradigm and model.