Infosys Intelligent Manufacturing Solutions
Overview
Tailored. Connected. Intelligent.
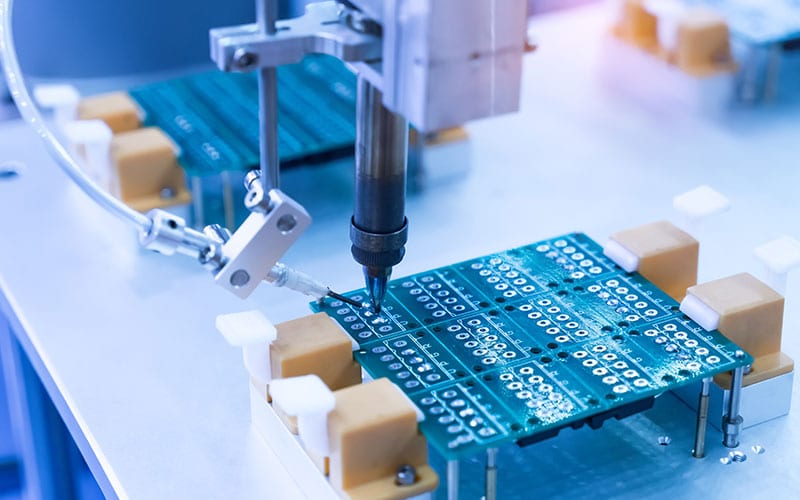
The path to smart manufacturing isn’t the same for all manufacturers. Different goals, challenges and systems call for unique approaches and focused changes. The Infosys IIoT Maturity Assessment Framework and our Connected Operations on Cloud solution help you map your own path to a smarter, connected shopfloor and unlock efficiencies precisely where you need them.
Infosys Smart Manufacturing brings a structured approach to shop floor transformation by studying your needs, processes, and digital maturity. The goal: A connected factory designed to deliver visibility, collaboration and orchestration of equipment, people, and products around demand signals.
Infosys Smart Manufacturing connects people, processes, and systems to deliver an intelligent manufacturing shop floor.
Talk to our experts
Challenges & Solutions

Request for services
Find out more about how we can help your organization navigate its next. Let us know your areas of interest so that we can serve you better.