About Infrastructure Security
With Hybrid mode of operations post pandemic, workplace being everywhere, increased adoption of cloud and digital technologies have meant greater agility and flexibility for organizations, with increased in attack surface which significantly enhanced security risks and vulnerabilities.
What's Happening
Our Offerings
Our Infrastructure Security service protects our clients’ perimeter, network, platforms, servers, databases, endpoints etc. with deep competence and Industry-tested Policies and Use Cases.
Other Solutions
Network Protection
Plan, design, deploy, configure, integrate, and manage network protection controls including Nex-Gen Firewalls, SDN Security, DDoS Protection, IPS, VPN, NAC, Network Authentication & Micro Segmentation solutions to protect IT assets
Workplace/ Workload Protection
Plan, design, deploy, configure, integrate, and manage host/OS & workload (VM, containers, etc.) security controls including OS Hardening, Host Anti-Virus, Anti-Malware, Host IPS, Host Firewall, EDR, Application Whitelisting, and File Integrity Monitoring solutions to secure hosts and OS of Mobiles, Endpoints, PoS systems
Secure Web Gateway
Plan, design, deploy, configure, integrate, and manage web access protection controls including Forward Proxy with URL filtering, Anti-Virus, Anti-Malware, Content Filtering, and SSL Inspection solutions
Secure Remote Access
Design, deploy, configure, and manage secure Remote Access VPN gateway solutions
Secure E-mail gateway
Design, deploy, configure, integrate, and manage e-mail protection controls including E-Mail Gateways with Anti-Phishing, Anti-Virus, Anti-Malware, Content Filtering, E-Mail Encryption & DMARC Security solutions
Advanced Threat Protection
Design, deploy, configure, integrate, and manage Advanced Threat Protection controls, including ATP and Sandboxing solutions
SASE with ZTNA
Design, deploy, configure, integrate, and manage organizations from perimeter-based security to SASE cloud-based service with Zero Trust Network Access
Micro-Segmentation
Design, deploy, configure, integrate, and manage micro-segmentation to ensure strict segmentation and policy enforcement is applied to workloads and protect from lateral spread of Security threats
Success Stories
Enhance your cyber defense by bringing cybersecurity skills-at-scale and deploying best in class protection controls and operational capabilities
Insights For You
Get a deeper understanding of our Infrastructure Security service offering
View All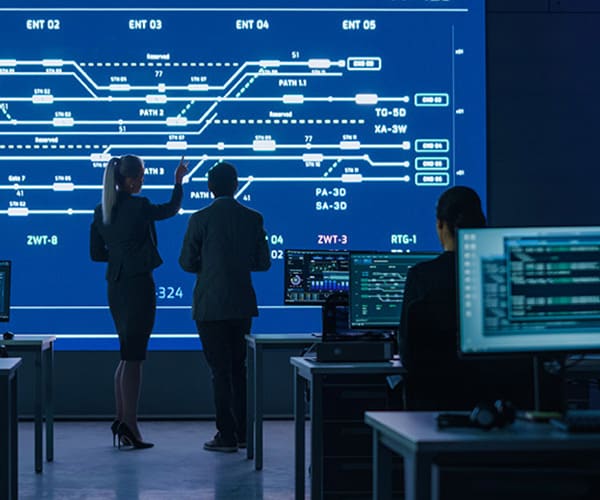
How we can help
Helping the enterprises in securing their infrastructure while transforming digitally
Enhanceperimeter network security for cloud, data center, branch/edge and plants
We plan, design, deploy and manage network security with nextgen firewalls and micro-segmentation to defend enterprises by applying enhanced and standardized security policies and gaining visibility across the network thus providing capability to security teams to swiftly detect and combat attacks through perimeters
SASE as a service
We navigate cloud first and internet first strategy execution by transformation with Infosys SASE as-a service solution. With Infosys SASE in collaboration with leading technology partners we migrate traditional on-premises proxy, VPN, cloud firewall, DLP, etc. to cloud-based capability along with delivering Zero Trust Network Access
Protect organizations from advanced and zero day attacks propagated through e-mails
A major part of electronic mail nowadays consists of unwanted messages & flood of usual spam and virus mails. Companies and employees now increasingly find themselves facing complex threats, such as social engineering and p attacks. Traditional security mechanisms often no longer provide sufficient protection from these personalized e-mails. We design, deploy, configure, integrate, and manage e-mail sSecurity solutions, including ATP and sandboxing solutions

Request for services
Find out more about how we can help your organization navigate its next. Let us know your areas of interest so that we can serve you better.