Operational Technology
Infosys's OT Security solutions, powered by Cyber AI NextGen SOC and Infosys Topaz, address these unique challenges. They provide enhanced visibility, proactive vulnerability mitigation, improved operational resilience, and effective cyber incident response. Prioritizing OT security is essential for maintaining safety and environmental protection, safeguarding assets, ensuring operational efficiency, and mitigating public safety risks in today's evolving threat landscape.
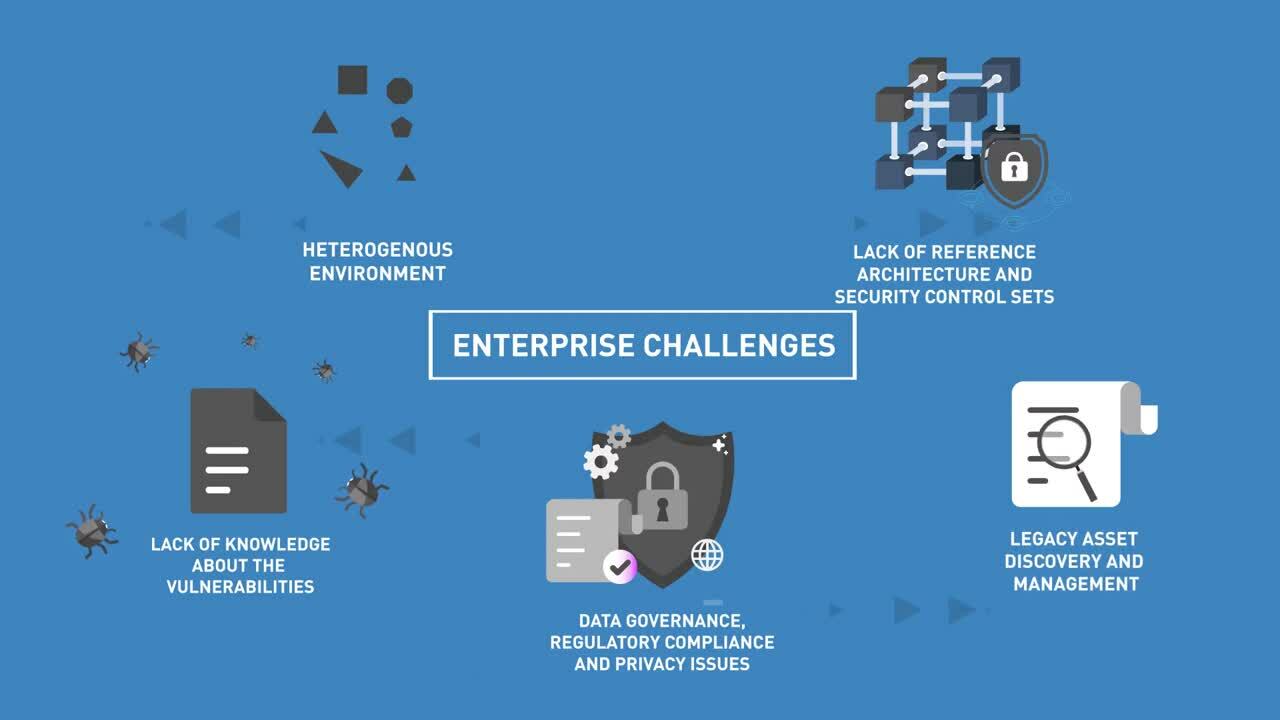
Operational Technology (OT) systems face increasing cybersecurity risks due to integration difficulties, legacy systems, skill gap, operational limitations, evolving compliance demands, and targeted and state sponsored attacks, which can lead to significant disruptions causing safety and environmental impact as well as financial losses and reputational damage.
Infosys' OT Security solutions, powered by Cyber AI and Infosys Topaz, amplifies our ability to tackle the unique and evolving challenges within Industrial Control Systems (ICS) and Industrial IoT (IIoT) environments.
We leverage Infosys Cyber AI and our Cyber Next Platform to provide intelligent and adaptive threat detection, going beyond traditional rule-based systems to identify subtle anomalies and sophisticated attacks in real-time across the OT environment. This enables proactive vulnerability mitigation by predicting potential attack vectors and recommending pre-emptive security measures.
Our AI-first set of services, solutions, and platforms injects next-gen automation and insights into OT security operations. This enhances visibility across complex OT landscapes, providing a unified and comprehensive view of assets and potential risks. We strengthen operational resilience by enabling faster and more efficient recovery from cyber incidents, for streamlined cyber incident response and quicker containment, remediation, and restoration of critical operations.
By harnessing the combined power of Cyber AI and Infosys Topaz, we empower organizations to elevate our clients’ OT security posture, ensuring safety, environment, robust safeguarding of assets, sustained operational efficiency, and effective mitigation of critical public safety risks in today's dynamic and increasingly hostile cyber landscape.
Infosys' Holistic OT Security Approach
-
Strategic OT security planning aligned with cyber initiatives and business outcomesWe ensure cybersecurity investments support long-term business goals, enabling secure innovation and operational excellence.
-
Proactive risk reduction by minimizing OT attack surface with smart segmentationWe enhance cyber resilience by limiting lateral movement, improving asset visibility, enabling network micro/segmentation, and reducing exposure to targeted attacks.
-
Governance-first cybersecurity for a compliant and scalable OT environmentWe establish a strong foundation for regulatory compliance (NIST 800-82, IEC 62443, NIS2.0, C2M2, DoE, NCA, etc.) while enabling scalable governance across industrial environments.
-
Converged security architecture enabling safe IT/OT integrationWe support digital transformation by securely bridging the IT and OT security gaps, ensuring operational continuity and reduced risk of integration.
-
Intelligent threat detection with real-time visibility across OT environmentsWe leverage NextGen SOC, Infosys Topaz, AI, and MITRE ATT&CK analytics to proactively detect and respond to threats, minimizing downtime and protecting critical infrastructure.

Request for services
Find out more about how we can help your organization navigate its next. Let us know your areas of interest so that we can serve you better.